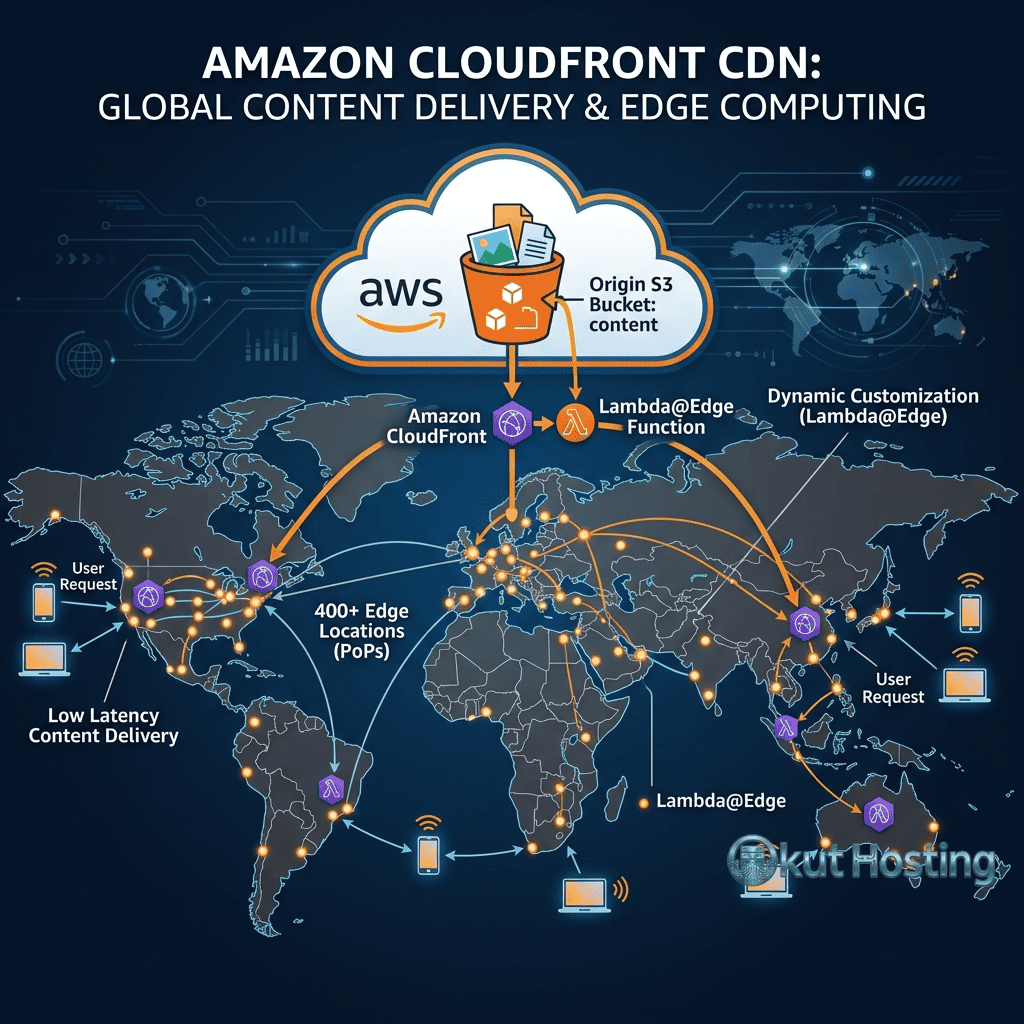
Amazon CloudFront is Amazon Web Services’ content delivery network service that distributes content through a global network of edge locations and regional edge caches. As a core component of the AWS ecosystem, CloudFront integrates deeply with other AWS services including S3 (object storage), EC2 (compute), Elastic Load Balancing, AWS Shield (DDoS protection), AWS WAF (web application firewall), and Lambda@Edge (edge computing). This tight ecosystem integration makes CloudFront a natural CDN choice for organizations already invested in AWS infrastructure, while its global scale and feature depth make it competitive as a standalone CDN for any website or application.
This review examines CloudFront’s network infrastructure, key features, pricing structure, security capabilities, edge computing through Lambda@Edge, WordPress compatibility, and competitive positioning. The analysis provides neutral evaluation for website owners and developers assessing CloudFront as their content delivery solution.
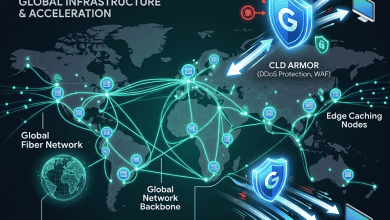
Global Edge Network
CloudFront operates one of the largest CDN networks globally, with over 400 Points of Presence (PoPs) including edge locations and regional edge caches across North America, Europe, Asia-Pacific, South America, the Middle East, Africa, and Oceania. The extensive network ensures low-latency content delivery to users worldwide, with edge locations positioned in major metropolitan areas and internet exchange points. Regional edge caches serve as intermediate caching layers between edge locations and origin servers, improving cache hit ratios for less-frequently accessed content that might be evicted from individual edge location caches.
CloudFront’s network is built on Amazon’s private backbone infrastructure, which provides optimized routing between edge locations and AWS origin services. This private network reduces latency and improves reliability compared to routing over the public internet. For websites hosted on AWS infrastructure (EC2, S3, Elastic Beanstalk), the private backbone provides particularly strong performance advantages through optimized origin-to-edge communication.
Origin Types and Configuration
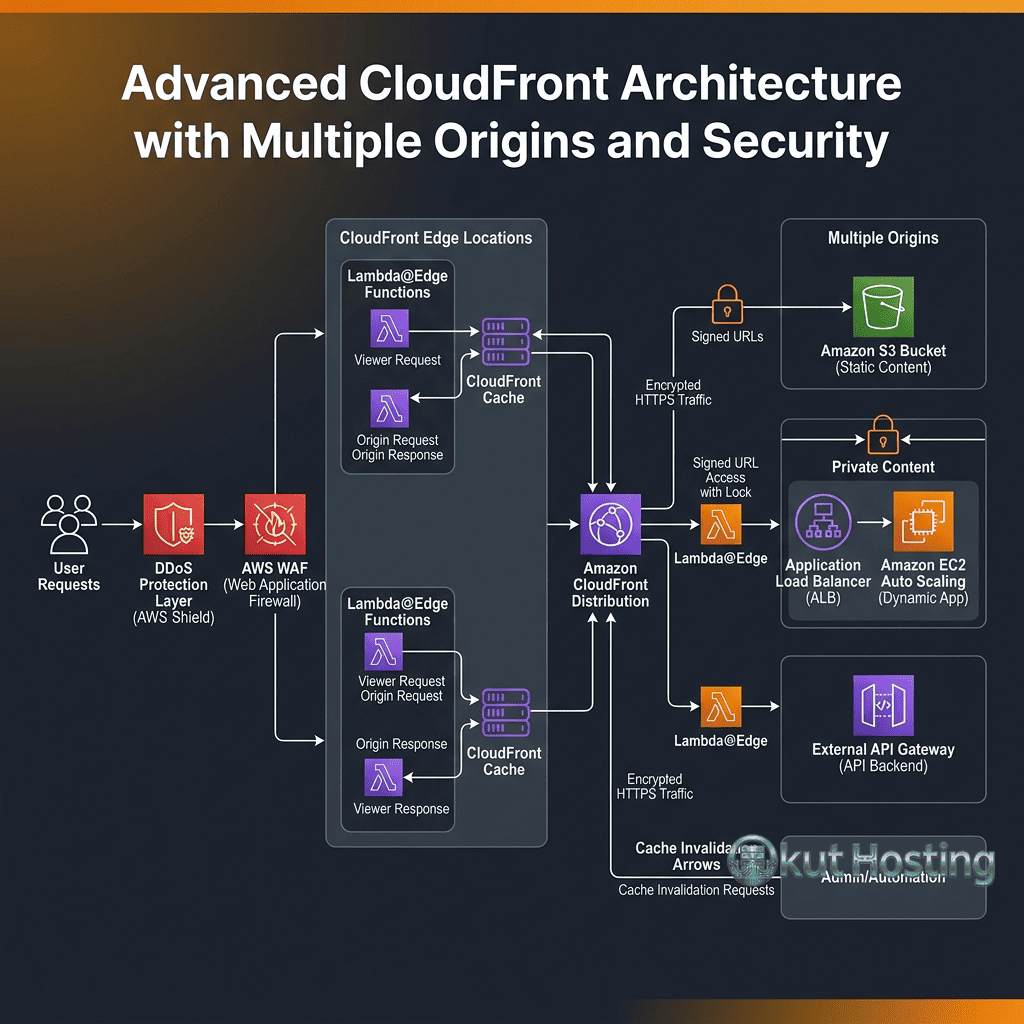
CloudFront supports multiple origin types for flexible content sourcing. Amazon S3 buckets serve as origins for static assets, enabling direct CDN delivery of files stored in S3 without requiring a web server. Custom origins (HTTP/HTTPS endpoints) enable CloudFront to cache and deliver content from any web server, including non-AWS hosting platforms. Origin groups provide failover capability by configuring primary and secondary origins, automatically switching to the secondary origin if the primary becomes unavailable.
Multiple origins can be configured within a single CloudFront distribution using path-based routing. For example, /images/* requests can be routed to an S3 origin while /api/* requests are routed to an application server origin. This multi-origin architecture enables sophisticated content delivery configurations that combine different backend services under a single CDN distribution.
Lambda@Edge
Lambda@Edge enables running serverless functions at CloudFront edge locations, executing custom code in response to CloudFront events (viewer request, viewer response, origin request, origin response). Lambda@Edge functions can modify requests and responses, implement authentication and authorization logic, generate synthetic responses, perform A/B testing, and customize content based on viewer attributes — all at the edge without routing requests to the origin server.
Lambda@Edge supports Node.js and Python runtimes, with execution time limits and memory allocations that vary by event type. Common use cases include: modifying HTTP headers for security or caching control; implementing URL rewriting and redirect logic; generating dynamic responses for simple API endpoints; performing geographic content customization; and implementing token-based authentication at the edge. Lambda@Edge provides powerful edge computing capabilities, though CloudFront Functions (a lighter-weight alternative) handles simpler request/response manipulations at higher throughput and lower latency.
CloudFront Functions
CloudFront Functions is a lightweight edge computing option designed for high-volume, low-latency request/response manipulations. CloudFront Functions execute in a JavaScript runtime with sub-millisecond startup times and can process millions of requests per second. Suitable use cases include: URL rewriting and normalization; header manipulation; cache key customization; request validation; and simple redirect logic. CloudFront Functions complement Lambda@Edge by handling simple, high-throughput operations more efficiently while Lambda@Edge handles more complex logic requiring longer execution times and more resources.
Pricing Structure
CloudFront pricing is based on data transfer out (per GB, varying by geographic region), HTTP/HTTPS request counts, and optional feature usage (Lambda@Edge invocations, field-level encryption, real-time logs). CloudFront offers a free tier that includes 1 TB of data transfer out, 10 million HTTP/HTTPS requests, and 2 million CloudFront Functions invocations per month for the first year. The pricing structure uses tiered rates where per-GB costs decrease as monthly volume increases, providing natural cost optimization for high-traffic websites.
CloudFront’s pricing can be optimized through: AWS Free Tier utilization for new accounts; Reserved Capacity pricing commitments for predictable high-volume usage; CloudFront Security Savings Bundle combining CloudFront with AWS WAF at discounted rates; and Origin Shield to reduce origin fetch costs. For websites with predictable traffic, reserved capacity pricing provides significant savings over on-demand rates.
Security Integration
CloudFront integrates with AWS’s comprehensive security services. AWS Shield Standard provides automatic DDoS protection at no additional cost, mitigating common network and transport layer attacks. AWS Shield Advanced (paid service) provides enhanced DDoS protection with real-time attack visibility, 24/7 DDoS response team access, and cost protection for scaling during attacks.
AWS WAF (Web Application Firewall) integrates directly with CloudFront to provide application-layer security including managed rule groups for common vulnerabilities (OWASP Top 10, bot protection, SQL injection), custom rules based on request attributes, rate-based rules for preventing brute force attacks, and geographic restrictions. The WAF integration enables comprehensive security at the CDN edge without requiring separate security infrastructure.
SSL/TLS and HTTPS
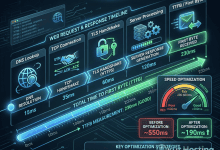
CloudFront provides free SSL/TLS certificates through AWS Certificate Manager (ACM) for custom domain names, with automatic certificate renewal. CloudFront supports TLS 1.3, Server Name Indication (SNI), and dedicated IP custom SSL for legacy client compatibility. SSL/TLS configuration options include security policies that define minimum TLS versions and supported cipher suites, enabling compliance with specific security requirements. The free ACM certificates eliminate SSL certificate costs for CloudFront distributions.
Caching Behavior
CloudFront’s caching behavior is highly configurable through cache policies and origin request policies. Cache policies define how CloudFront caches content based on URL query strings, HTTP headers, and cookies. Origin request policies control which request elements are forwarded to the origin server. This separation of caching and origin request configurations enables sophisticated caching strategies that maximize cache hit ratios while ensuring the origin receives necessary request information.
Cache invalidation enables purging specific objects or path patterns from all edge locations. While cache invalidation is effective for removing stale content, CloudFront charges for invalidation requests beyond a monthly free allocation (1,000 paths per month). Using versioned URLs (asset-v2.js) rather than cache invalidation is recommended as a cost-effective alternative for managing content updates.
Real-Time Metrics and Logging
CloudFront provides detailed metrics through Amazon CloudWatch, including request counts, bytes transferred, error rates, and cache hit ratios. CloudFront real-time logs stream request-level data to Amazon Kinesis Data Streams for real-time analysis. Standard access logs are delivered to S3 buckets for batch analysis. The combination of real-time metrics, real-time logs, and standard logs provides comprehensive visibility into CDN performance and usage patterns.
WordPress Compatibility
CloudFront is compatible with WordPress through CDN integration plugins (W3 Total Cache, WP Super Cache, CDN Enabler) or through reverse proxy configuration. For WordPress sites hosted on AWS (EC2, Lightsail), CloudFront integration provides performance optimization with minimal network overhead due to the private backbone connection. For WordPress sites hosted outside AWS, CloudFront functions as a standard CDN with content pulled from the external origin.
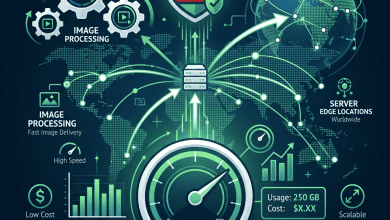
S3 Static Website Hosting
CloudFront combined with S3 provides a highly scalable, serverless static website hosting solution. S3 serves as the origin storing HTML, CSS, JavaScript, and media files, while CloudFront provides global edge delivery, HTTPS support, and custom domain configuration. This architecture eliminates the need for web servers entirely, providing virtually unlimited scalability at storage and bandwidth costs. Static site generators (Hugo, Jekyll, Gatsby) commonly deploy to S3 + CloudFront for high-performance, low-cost website hosting.
Geographic Restrictions
CloudFront supports geographic restrictions (geo-blocking) that allow or deny content access based on the viewer’s country. Geographic restrictions are configured at the distribution level and use MaxMind’s GeoIP database for country identification. This feature supports content licensing compliance, regulatory requirements, and targeted content distribution. For more granular geographic logic, Lambda@Edge or CloudFront Functions can implement region-based or city-based routing decisions.
Origin Access Control
Origin Access Control (OAC) restricts S3 origin access to CloudFront distributions only, preventing direct S3 access that would bypass CDN caching and security controls. OAC ensures that all content access flows through CloudFront, maintaining consistent security policies, access logging, and caching behavior. This feature is essential for S3-hosted content where direct origin access should be prevented for security, cost, or compliance reasons.
Origin Shield
CloudFront Origin Shield adds an additional caching layer between edge locations and the origin server, consolidating origin requests through a single cache layer. Origin Shield reduces the number of requests reaching the origin by serving as a centralized cache that edge locations query before contacting the origin. This feature is particularly valuable for: origins with limited capacity or high per-request costs; websites with content accessed from many geographic regions; and architectures where minimizing origin load is critical for performance or cost management. Origin Shield’s cache hit ratio improvements can significantly reduce origin server costs and improve response times for cache miss scenarios.
Video Streaming
CloudFront supports multiple video streaming protocols including HTTP Live Streaming (HLS), Dynamic Adaptive Streaming over HTTP (DASH), Microsoft Smooth Streaming, and CMAF (Common Media Application Format). For live streaming, CloudFront integrates with AWS Elemental MediaLive and MediaPackage for professional broadcast-quality live video delivery. For on-demand video, CloudFront delivers pre-encoded video files from S3 origins with adaptive bitrate streaming. The combination of CloudFront’s global edge network and AWS Elemental media services provides enterprise-grade video delivery infrastructure.
Field-Level Encryption
CloudFront’s field-level encryption feature enables encrypting specific form data fields at the edge before forwarding requests to the origin server. This ensures that sensitive data (credit card numbers, personal information) is encrypted beyond standard HTTPS encryption, remaining encrypted through CloudFront’s infrastructure and at the origin until explicitly decrypted by the application using private keys. Field-level encryption adds a defense-in-depth layer for sensitive data handling that exceeds standard TLS protection.
Signed URLs and Signed Cookies
CloudFront supports signed URLs and signed cookies for restricting access to private content. Signed URLs provide time-limited access to specific content, commonly used for paid content, software downloads, and temporary file sharing. Signed cookies provide time-limited access to multiple content items, commonly used for subscription-based content where users access multiple pages or assets during an authenticated session. Both mechanisms use RSA key pairs for cryptographic verification, preventing unauthorized access to restricted content.
Continuous Deployment
CloudFront’s continuous deployment feature enables testing configuration changes on a percentage of production traffic before full deployment. This canary-style deployment approach reduces the risk of configuration changes by validating behavior with a small traffic sample. If the new configuration performs correctly, it can be promoted to handle all traffic; if issues are detected, the configuration can be rolled back without impacting the majority of visitors. This testing capability brings software deployment best practices to CDN configuration management.
Cost Optimization Strategies
CloudFront cost optimization involves multiple strategies: using the appropriate price class (limiting edge locations to reduce costs for traffic concentrated in specific regions); implementing efficient caching policies that maximize cache hit ratios; using versioned URLs instead of cache invalidation to avoid invalidation charges; leveraging CloudFront Functions instead of Lambda@Edge for simple operations (CloudFront Functions are significantly cheaper); enabling compression to reduce data transfer costs; and using the CloudFront Security Savings Bundle for combined CDN and WAF pricing discounts.
Infrastructure as Code
CloudFront distributions can be managed through Infrastructure as Code tools including AWS CloudFormation, Terraform, AWS CDK (Cloud Development Kit), and Pulumi. IaC management enables version-controlled CDN configurations, reproducible deployments across environments, automated testing of configuration changes, and audit trails for all infrastructure modifications. For organizations managing multiple CloudFront distributions or requiring consistent configurations across environments, IaC provides essential configuration management capabilities.
Monitoring and Alerting
CloudFront’s CloudWatch integration provides comprehensive monitoring with configurable alerts. Key metrics available for monitoring include: total requests, error rates (4xx and 5xx), bytes downloaded and uploaded, cache hit ratio, and origin latency. CloudWatch Alarms can trigger notifications through SNS (Simple Notification Service) when metrics exceed defined thresholds, enabling proactive response to performance degradation, error spikes, or unusual traffic patterns. Custom dashboards combining CloudFront metrics with origin server metrics provide holistic infrastructure visibility.
Multi-Region Architecture
For globally distributed applications, CloudFront enables multi-region architectures where origin servers in different AWS regions serve as primary origins for specific geographic areas, with failover to alternative regions if the primary becomes unavailable. Combined with Route 53 (AWS DNS with geographic routing) and Application Load Balancer, CloudFront enables sophisticated multi-region content delivery architectures that optimize performance and resilience for global audiences.
Comparison with Competitors
Compared to Cloudflare, CloudFront provides deeper AWS ecosystem integration and more origin configuration flexibility, while Cloudflare provides a free tier without time limitations, simpler configuration, and a larger edge network. Compared to Fastly, CloudFront provides broader geographic coverage and AWS integration, while Fastly provides instant cache purging, more powerful VCL configuration, and real-time analytics. Compared to BunnyCDN, CloudFront provides more features and AWS integration, while BunnyCDN provides simpler pricing and easier configuration.
Compliance and Certifications
CloudFront operates within AWS’s comprehensive compliance framework, inheriting certifications including SOC 1/2/3, PCI DSS Level 1, HIPAA eligibility, ISO 27001, ISO 27017, ISO 27018, FedRAMP, and GDPR compliance. These certifications enable CloudFront deployment in regulated environments including healthcare, financial services, government, and education. For organizations with strict compliance requirements, CloudFront’s certification portfolio and AWS’s compliance documentation provide the assurance needed to include CDN infrastructure in compliant architectures. The breadth of AWS compliance certifications exceeds most competing CDN providers.
Limitations and Considerations
CloudFront’s primary limitations include: configuration complexity compared to simpler CDN services (Cloudflare, BunnyCDN); per-invalidation charges that can add costs for frequently updated content; slower cache purge propagation compared to Fastly’s instant purge; and an AWS-centric interface that may be unfamiliar to users without AWS experience. The learning curve for CloudFront configuration, particularly for Lambda@Edge development, is steeper than simpler CDN alternatives. However, these tradeoffs reflect CloudFront’s greater flexibility and deeper feature set.
Summary
Amazon CloudFront provides enterprise-grade content delivery through a massive global edge network with deep AWS ecosystem integration, powerful edge computing through Lambda@Edge and CloudFront Functions, comprehensive security through AWS Shield and WAF integration, and flexible origin configuration supporting multiple content sources. CloudFront excels for organizations using AWS infrastructure, websites requiring sophisticated edge computing capabilities, and applications needing enterprise-scale content delivery with robust security. The platform’s complexity and pricing structure may be excessive for simple websites, but for organizations requiring CloudFront’s capabilities, the platform provides reliable, scalable, and highly configurable content delivery.
Features, pricing, and availability discussed in this review reflect information available at the time of writing. Please verify current details on the official AWS CloudFront website. Okut Hosting is an independent review platform with no affiliate relationships with any company mentioned in this article.
For related reviews, see our Cloudflare vs BunnyCDN comparison, our Google Cloud CDN review, and our Akamai CDN review.